Why Cybersecurity Awareness Matters in October and All Year Round

In October, not just the vibrant hues of autumn deserve our attention. This month is designated as Cybersecurity Awareness Month, emphasizing the crucial need to safeguard our digital lives. Yet, it’s imperative to remember that cybersecurity is a year-round concern, like how we cherish our loved ones consistently, not just on special occasions like Valentine’s […]
Applying Martial Arts Principles to Cybersecurity Practices
In the realm of cybersecurity, the ability to anticipate, adapt, and respond swiftly to threats is paramount. Much like the martial art of Jiu-Jitsu, which emphasizes leverage, strategy, and adaptability, cybersecurity professionals can draw significant parallels in their approach to safeguarding digital landscapes. Adaptability and Situational Awareness Jiu-Jitsu teaches practitioners to be aware of their […]
Cultivating Cybersecurity Champions: The Power of Character, Capability, and Commitment
In the ever-evolving cybersecurity landscape, finding suitable candidates to defend against the constant barrage of cyber threats has become challenging. The issue perpetuates largely from employers setting unrealistic expectations, rather than people unwilling do the work. The field demands individuals with technical skills, the right mindset, and the commitment to make a real impact. The […]
The Hiring Crisis in Cybersecurity: Addressing the Knowledge Gap and Fostering Growth

In recent years, the field of cybersecurity has seen exponential growth and demand. Social media has been flooded with advertisements for cybersecurity positions, reflecting the urgent need for skilled professionals to safeguard digital assets. Many outlets report a shortage of cybersecurity professionals. However, this shortage is not due to a lack of talent. Rather, it’s […]
Unlocking Careers in Cybersecurity: Your First Steps into the Field

Cybercriminals launch new advanced computer viruses, malware, and phishing campaigns every day that threaten the data our society relies on. If you have a passion for technology, the drive to learn continuously, and the desire to make a difference, a career in cybersecurity could be the perfect fit for you. However, before you jump headfirst […]
Security for All, Not Some: Safeguarding the Unconnected
At a recent event, multiple companies asked if you really need to protect air-gapped technology, and, if so, how to do it. It’s easy to assume that if a system is air-gapped or not connected to the network, it’s inherently safe from cyber threats. However, this is a dangerous misconception. Even in isolation, no system […]
Defending Against the Unseen: How BLOKWORX Utilizes Deep Instinct for Cutting-edge Prevention
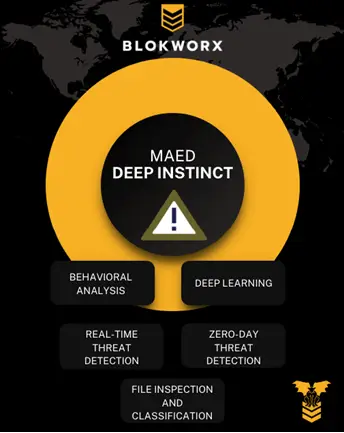
In today’s interconnected digital landscape, cybersecurity threats continue to evolve at an alarming rate. Malicious actors constantly seek new ways to exploit vulnerabilities and infect systems with malware. As a result, innovative technologies like Deep Instinct play a crucial role in combating this ever-growing menace. Recently, Deep Instinct uncovered a new JavaScript-based malware dropper, as […]
The Power of Prevention: How BLOKWORX Services Safeguard Against the Microsoft Teams Bug

A recent vulnerability in Microsoft Teams has emphasized the power of prevention-centric cybersecurity. This bug enables malware delivery from external accounts. This poses a significant threat to businesses that are not appropriately aware and prepared. BLOKWORX services provide a comprehensive prevention-centric security approach designed to effectively safeguard against these vulnerabilities. As discussed in reports from […]
The Crucial Role of Vulnerability Scans

In today’s digital landscape, both protected and unprotected environments face numerous cybersecurity challenges. Managed Service Providers (MSPs) play a vital role in safeguarding these environments, utilizing security services such as endpoint protection, email security, and firewalls. However, incorporating vulnerability scans (note: significantly different than penetration tests) is equally crucial. The indispensable role of vulnerability scans for […]
Protect Against the Dangers of .zip and .mov Domains

The introduction of new top-level domains (TLDs) by Google Registry, including .zip and .mov, has raised concerns within the infosec community regarding cybersecurity risks. Deep learning and machine learning can be vital in preventing and mitigating these risks. Additionally, users must understand these dangers and take the necessary steps to protect themselves. The .zip TLD […]
Deep Learning vs. Machine Learning
Deep learning and machine learning are both branches of artificial intelligence (AI). They involve building algorithms to analyze and make predictions or decisions based on data. However, there are some significant differences between the two methodologies. Deep Learning Deep learning involves building and training artificial neural networks that are capable of learning from large amounts […]
Sales Tools vs. Actual Security: Differentiating Between Scans
Imagine you’ve just purchased a certified used car. As part of due diligence, you take that car into another dealership for a full workup. That dealership tells you that you have $9,000 in repair work before the vehicle should be considered drivable. You return to the dealership that sold you the “lemon” understandably peeved […]
