Cybersecurity
Glossary
QUESTIONS & ANSWERS
Frequently Asked Questions
What is an MSSP?
An MSSP (Managed Security Service Provider) is a third-party organization that offers a comprehensive range of security services to businesses. These services often include managing and monitoring security devices such as firewalls, providing endpoint protection, detecting and responding to security incidents, and overseeing security operations centers (SOCs).
What types of security services does your MSSP offer?
BLOKWORX (MSSP) offers a wide array of security services, including endpoint security to protect devices such as computers and mobile devices, cloud security to secure data and applications hosted in the cloud, firewall management to safeguard network perimeters, threat detection to identify and respond to cyber threats, and SOC services to oversee security operations and incident response.
How does endpoint security protect my devices?
Endpoint security solutions are designed to protect individual devices, such as computers and mobile devices, from various cyber threats. This includes malware protection, firewall management, intrusion detection, data encryption, and vulnerability assessments. By deploying endpoint security solutions, we ensure that your devices are shielded from potential threats and vulnerabilities.
How do you manage and monitor firewalls?
Our firewall management services involve configuring, monitoring, and maintaining firewall devices to protect your network from unauthorized access and cyber threats. This includes implementing firewall rules, conducting regular security assessments, and responding to firewall-related incidents promptly to ensure the security of your network infrastructure.
What is threat detection, and how does it work?
Threat detection involves continuously monitoring your network and endpoints for signs of suspicious or malicious activity. This includes analyzing network traffic, logs, and endpoint behavior to identify potential security threats such as malware infections, unauthorized access attempts, and data breaches. Once a threat is detected, our team responds swiftly to mitigate the risk and prevent further damage.
What role does the SOC play in your security services?
Our 24/7/365 US – Based Security Operations Center (SOC) serves as the central hub for monitoring, detecting, and responding to security incidents. Our team of security analysts works around the clock to analyze security alerts, investigate potential threats, and coordinate incident response efforts. The SOC plays a critical role in ensuring the effectiveness of our security services and protecting your organization from cyber threats.

Stop Playing Defense: Why 16 Billion Stolen Credentials Prove Prevention Must Come First
How BLOKWORX Scales Prevention-First Security: A Partnership That Changes Everything

The Endpoint Security Wake-Up Call: Why Your Current Defense Strategy Is Failing

Words & Definitions
Defined Key Phrases
Managed Endpoint Protection (MAED)
A comprehensive solution focusing on preventing threats at the endpoint level using deep learning technologies. MAED emphasizes “Zero-Time” prevention, which allows for the blocking of unknown threats and new variants without the need for analysis post-alert. It aims to reduce false positives and ensure minimal resource interruption.
Endpoint Detection and Response (EDR)
A cybersecurity technology designed to monitor endpoint activities and detect and respond to threats. EDR enhances data telemetry to improve the response to incidents, providing detailed visibility into endpoint behavior and facilitating rapid reaction to potential threats.
Secure Cloud Unified Defense (SCUD)
SCUD is a service designed to provide advanced threat protection for cloud environments. It connects to cloud email and collaboration apps, scanning for threats after existing security but before reaching the inbox. SCUD offers protection against phishing, malware, insider threats, and business email compromise, all managed and supported 24/7 by Blokworx’s US-based SOC.
Secure Network Perimeter Response (SNPR)
SNPR is a fully-managed firewall service that offers enterprise-level edge security. It includes the deployment and management of Next Generation Firewalls, supported by 24/7 monitoring and incident response from Blokworx’s SOC. SNPR protects against network threats and vulnerabilities, ensuring a dynamic security posture through continuous monitoring and updates
Managed Firewall Service
A service that includes the configuration, engineering, migration, deployment, and management of next-generation firewalls. This service aims to protect an organization’s network by ensuring proper firewall setup and continuous monitoring to defend against intrusions and threats
Secure Access Service Edge (SASE)
A security model that moves traditional firewall functionalities to the cloud, providing secure and compliant network access for businesses. SASE integrates wide-area networking with comprehensive security services, including secure web gateways, CASB, and zero-trust network access.
Extended Detection and Response (XDR)
A holistic security approach that collects and correlates data across multiple security layers – including endpoints, servers, and networks – to improve threat detection and response capabilities. Managed XDR platforms provide logging, data retention, reporting, telemetry, and response functionalities across an organization’s IT environment.
Threat Hunting
A proactive cybersecurity practice that involves searching through networks to detect and isolate advanced threats that evade existing security solutions. Threat hunting leverages automated alerts supported by human analysis to identify and mitigate potential threats before they cause harm.
Security Operations Center (SOC)
A centralized unit that deals with security issues on an organizational and technical level. A managed SOC offers 24/7 monitoring and incident response services to protect against cyber threats, ensuring continuous vigilance and rapid reaction to any security incidents.
Attack Surface Mitigation
The process of identifying and reducing the number of potential entry points for cyber attackers. This involves regular vulnerability scanning and implementing recommendations for remediation and mitigation to enhance an organization’s security posture.
Cloud Security
A collection of technologies, policies, controls, and services designed to protect cloud-based systems, data, and infrastructure from cybersecurity threats. Cloud security encompasses securing cloud access, data integrity, and ensuring compliance with regulatory standards.
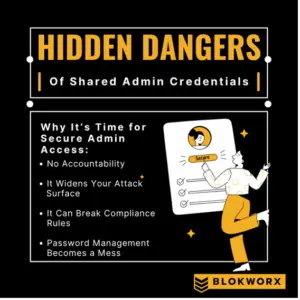
Zero Trust Architecture
A security framework that assumes no implicit trust within the network, whether internal or external. Zero Trust requires strict identity verification for every person and device trying to access resources on a private network, minimizing the attack surface and mitigating risks of data breaches.
Behavioral Analysis
A technique used in cybersecurity to detect anomalies and potential threats by analyzing patterns of behavior within an IT environment. Behavioral analysis helps in identifying unusual activities that may indicate a security incident, even if specific threats are not recognized by traditional security tools.
Deep Learning Endpoint Technology
An advanced form of artificial intelligence used in cybersecurity to improve threat detection and prevention at the endpoint level. This technology continuously learns from data, enhancing its ability to identify and block new and evolving threats in real-time.
White Glove Onboarding
A high-touch, personalized onboarding process where cybersecurity providers ensure a seamless transition and setup of their services. This includes thorough planning, implementation, and tuning of security solutions to meet the specific needs of the client.
Incident Response
The structured approach taken by an organization to handle and manage the aftermath of a security breach or cyberattack. The goal is to effectively contain the incident, minimize damage, and reduce recovery time and costs.
Next Generation Firewall (NGFW)
An advanced firewall that goes beyond traditional firewall functionalities by integrating additional features like deep packet inspection, intrusion prevention, and application awareness. NGFWs provide more comprehensive security by addressing modern threats and vulnerabilities.
Threat Intelligence
The analysis of data regarding threats and threat actors to better understand and mitigate potential cyber risks. Threat intelligence includes collecting information from various sources to anticipate and defend against cyber threats proactively.
Acronyms & Descriptions
Deciphering Security Acronyms
PPSA (Public Policy and Safety Act)
A legislative framework focused on ensuring public safety through various regulations and policies.
API (Application Programming Interface)
A set of protocols, routines, and tools for building software and applications. APIs allow different software systems to communicate with each other.
CLI (Command Line Interface)
A text-based user interface used to interact with software and operating systems by typing commands.
EPP (Endpoint Protection Platform)
Security solutions that protect endpoint devices like computers and mobile devices from cyber threats.
GUI (Graphical User Interface)
A user interface that includes graphical elements, such as windows, icons, and buttons, making it easier for users to interact with electronic devices.
HaaS (Hardware as a Service)
A procurement model similar to leasing or licensing where hardware is provided and managed by a service provider.
IRaaS (Incident Response as a Service)
A service that provides organizations with the expertise to handle and mitigate security incidents, typically offered by a third-party provider.
SaaS (Software as a Service)
A software distribution model in which applications are hosted by a service provider and made available to customers over the internet.
OWA (Outlook Web App)
A web-based email client that is part of the Microsoft Exchange Server.
PUA (Potentially Unwanted Application)
Software that is not inherently malicious but may pose a risk to privacy or security.
EOS (End of Service)
A term used to describe when a product is no longer supported or serviced by the manufacturer.
FUD (Fear, Uncertainty, and Doubt)
A strategy used to influence perception by disseminating negative and dubious or false information.
MDR (Managed Detection and Response)
A cybersecurity service that provides organizations with threat hunting, monitoring, and response capabilities without the need to build or maintain their own security operations center.
AI (Artificial Intelligence)
The simulation of human intelligence in machines that are programmed to think and learn like humans.
POC (Proof of Concept)
A demonstration to verify that certain concepts or theories have the potential for real-world application.
MFA (Multi-Factor Authentication)
A security system that requires more than one method of authentication from independent categories of credentials to verify the user’s identity.
DLP (Data Loss Prevention)
A strategy for making sure that end users do not send sensitive or critical information outside the corporate network.
DNS (Domain Name System)
A hierarchical and decentralized naming system for computers, services, or other resources connected to the internet or a private network.
SOAR (Security Orchestration, Automation, and Response)
A set of tools that allows organizations to collect security data and alerts from different sources and automate the response process.
SIEM (Security Information and Event Management)
A solution that provides real-time analysis of security alerts generated by applications and network hardware.
RMM (Remote Monitoring and Management)
A type of software used by managed IT service providers to remotely and proactively monitor client endpoints, networks, and computers.



GET THE SITUATION REPORT
Stay informed about the latest in cybersecurity. Subscribe to The Situation Report to get the information you need to keep your business safe and your data secure.

