BLOG
In today’s interconnected digital landscape, cybersecurity threats continue to evolve at an alarming rate. Malicious actors constantly seek new ways to exploit vulnerabilities and infect systems...
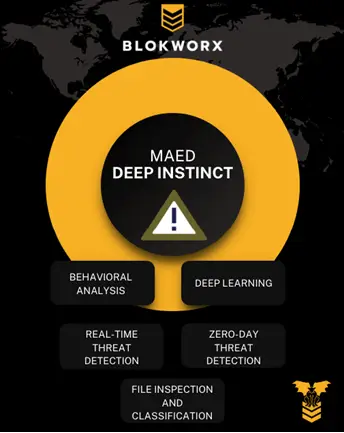
A recent vulnerability in Microsoft Teams has emphasized the power of prevention-centric cybersecurity. This bug enables malware delivery from external accounts. This poses a significant threat to...
In today’s digital landscape, both protected and unprotected environments face numerous cybersecurity challenges. Managed Service Providers (MSPs) play a vital role in safeguarding these...
The introduction of new top-level domains (TLDs) by Google Registry, including .zip and .mov, has raised concerns within the infosec community regarding cybersecurity risks. Deep learning and machine...
Deep learning and machine learning are both branches of artificial intelligence (AI). They involve building algorithms to analyze and make predictions or decisions based on data. However, there are...
Imagine you’ve just purchased a certified used car. As part of due diligence, you take that car into another dealership for a full workup. That dealership tells you that you have $9,000...
Ransomware continues to be a pressing cybersecurity threat, causing significant disruptions and financial losses for individuals, businesses, and municipalities. The recent 2023 Dallas ransomware...
Recently, we attended several industry events. Looking around the vendor halls, there were no less than 30 vendors providing cybersecurity tools. All of them presented value and hit different portions...
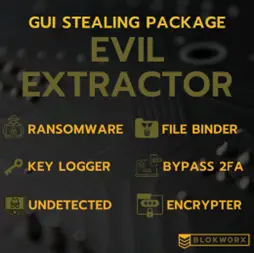
EvilExtractor malware extracts sensitive or confidential information from a victim’s computer system without their consent or knowledge. It falls under the category of information-stealing...